Investing in new technology for your business is no small decision. It is easy to get swayed by the latest fancy gadgets and special deals which can end up with buyer’s remorse especially when you don’t fully understand it and how it will fit into your business. Here are some key questions you need to ask and / or address before making that investment. Continue reading
Tag Archives: adelaide
People: The Human Firewall
Data security and privacy is not just a concern for large companies as it is crucial item for every business to consider. Imagine a scenario where a simple slip-up with sensitive information could lead to significant financial loss, damage to your reputation and / or legal issues. This can be scary, but do not worry, because you can safeguard your business by turning your employees into human firewalls. Here are some ways on how to do this: Continue reading
AI is Great, but be Careful!
If you’ve been using AI services such as Copilot or ChatGPT in your business, you will know how helpful it can be. Whether analysing a spreadsheet, summarising an email or generating ideas, these AI tools can save you time and effort. But, like any powerful tool, they come with their own risks. One big concern is how they learn from the data they are given. In this article we dive into why this is important and what you need to watch out for. Continue reading
What To Do When You Accidentally Send an Email to the Wrong Person
We have all accidentally sent an email to the wrong person? You can easily enter the wrong email address, autocompleted the incorrect contact, clicked “reply all” without realising who was on the CC list or chosen the wrong name from your contact list. Continue reading
Are You Losing Money Because Employees Can’t Use Technology?
Shiny new technology can be exciting for some people but can scare others! In todays world, new tech can be a must to stay competitive and it increased efficiency, happier employees and a competitive edge. That promise can turn into a financial nightmare if employees can’t use their technology. This can then cause productivity to drop, mistakes and customer service to fall. This blog shows the common staff technology issues as provides solutions. Continue reading
The Pros and Cons of Incognito Browsing
Many people are increasingly concerned about privacy, and your browser’s Private Browsing Mode (or Incognito Mode), offers a simple way to keep your online activities hidden from others who share your computer. Continue reading
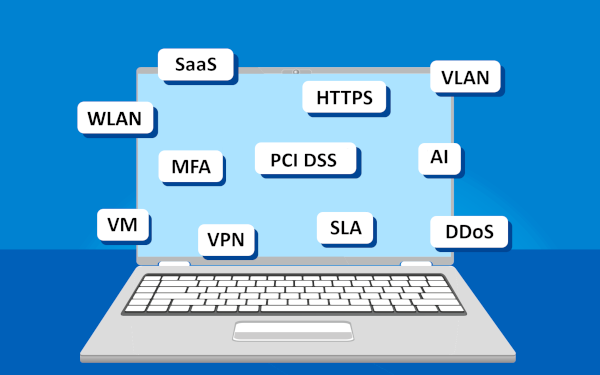
Are You Lost in The Cybersecurity Jungle: Don’t Go Unprepared!
Cybersecurity is like a jungle: a sprawling, bewildering landscape that businesses find hard to explore. As an IT Provider, we understand the uncertainty that comes with trying to navigate the complex world of cybersecurity. The jungle is vast, with threats hidden in the undergrowth if you set anything up incorrectly and the path to safety (and compliance) is not clear. Continue reading
4 Ways Small Businesses Can Leverage Copilot for M365
Efficiency, productivity, and innovation are some of the key differentiators that can propel small businesses forward. Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for growth. Continue reading
How To Spot Malicious Website URLs
When browsing the web, using social media or checking your email, it is very important to exercise caution when clicking on links. Cybercriminals actively create deceptive links to infect devices with malware or steal personal information. Continue reading
The Top Acronyms in Technology
We have all heard about some of the classic tech abbreviations by now, such as CPU and RAM. However, modern workplaces are introducing many new ones and below are some that you are most likely to see in today’s business world (check our our previous blog on Internet Lingo for some other terms). Continue reading