If you’ve been using AI services such as Copilot or ChatGPT in your business, you will know how helpful it can be. Whether analysing a spreadsheet, summarising an email or generating ideas, these AI tools can save you time and effort. But, like any powerful tool, they come with their own risks. One big concern is how they learn from the data they are given. In this article we dive into why this is important and what you need to watch out for. Continue reading
Category Archives: Tips & Tricks
What To Do When You Accidentally Send an Email to the Wrong Person
We have all accidentally sent an email to the wrong person? You can easily enter the wrong email address, autocompleted the incorrect contact, clicked “reply all” without realising who was on the CC list or chosen the wrong name from your contact list. Continue reading
Are You Losing Money Because Employees Can’t Use Technology?
Shiny new technology can be exciting for some people but can scare others! In todays world, new tech can be a must to stay competitive and it increased efficiency, happier employees and a competitive edge. That promise can turn into a financial nightmare if employees can’t use their technology. This can then cause productivity to drop, mistakes and customer service to fall. This blog shows the common staff technology issues as provides solutions. Continue reading
Are You Lost in The Cybersecurity Jungle: Don’t Go Unprepared!
Cybersecurity is like a jungle: a sprawling, bewildering landscape that businesses find hard to explore. As an IT Provider, we understand the uncertainty that comes with trying to navigate the complex world of cybersecurity. The jungle is vast, with threats hidden in the undergrowth if you set anything up incorrectly and the path to safety (and compliance) is not clear. Continue reading
4 Ways Small Businesses Can Leverage Copilot for M365
Efficiency, productivity, and innovation are some of the key differentiators that can propel small businesses forward. Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for growth. Continue reading
MS Recall – Microsoft’s New AI Feature
MS has introduced a new AI feature called “Recall” to Windows 11 which is designed to enhance your experience by acting as a virtual time machine. It will allow users to quickly find anything they have seen on a computer in the past. This blog article will show how it works and why we think it is useful. Continue reading
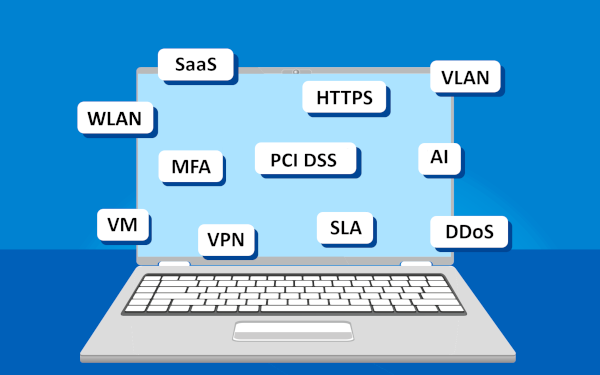
The Top Acronyms in Technology
We have all heard about some of the classic tech abbreviations by now, such as CPU and RAM. However, modern workplaces are introducing many new ones and below are some that you are most likely to see in today’s business world (check our our previous blog on Internet Lingo for some other terms). Continue reading
The Downsides of Buying a Cheap Printer
We have all been there – rushing to print an important document only to discover your cheap inkjet printer is playing up again. It may be refusing to print because the colour cartridges are empty, not feeding pages through properly or leaving streaks across your printouts. The cheap inkjet printers are notorious for acting up just when you need to print that urgent document. Beyond the frustration, these constant issues could be costing you more than you realise. Continue reading
Is It Time To Upgrade Your Internet Router?
Have you noticed your internet experience declining recently, do you have bad wireless coverage throughout your office or concerned about the security of your network? If so, it may be time for an upgrade. Continue reading